NetSec Platform: Cloud-Delivered Security Services
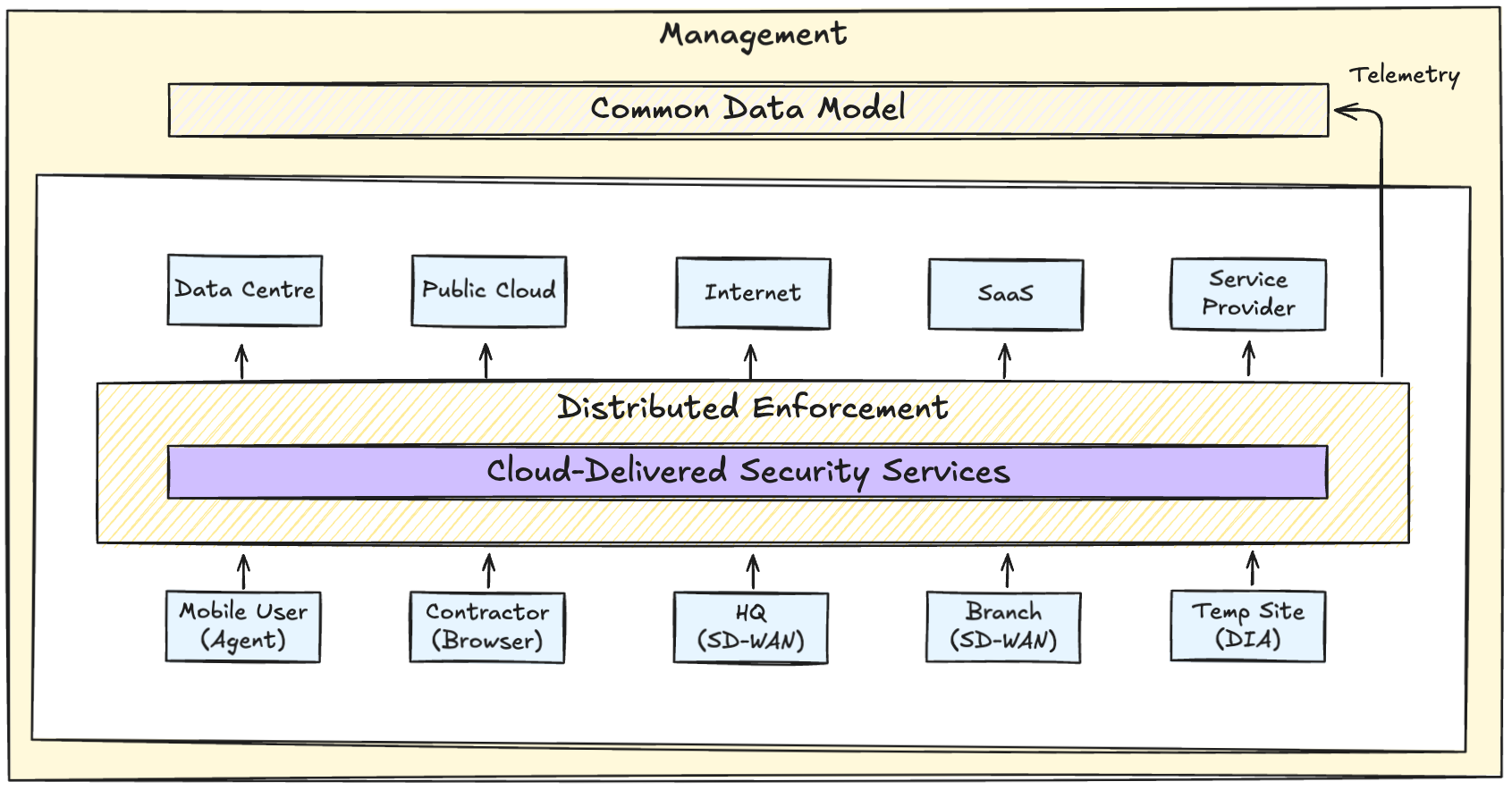
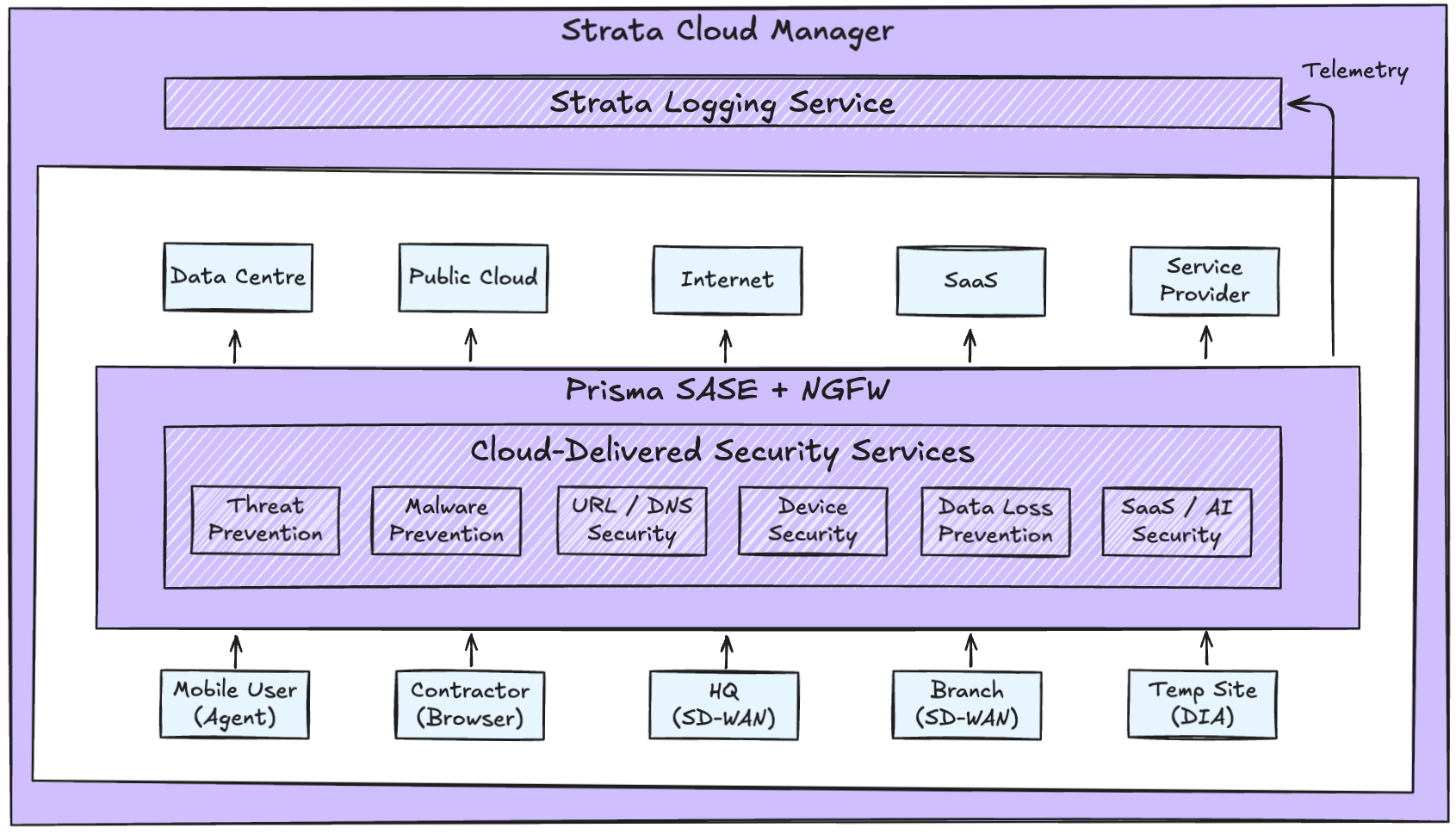
In the previous posts, Prisma Access was positioned as the distributed enforcement layer of the NetSec platform, with Strata Cloud Manager (SCM) operating as the central control plane for policy and visibility.
This post explains Cloud-Delivered Security Services (CDSS) - the shared inspection layer that provides detection and prevention capabilities across enforcement form factors.
These services are delivered centrally and applied consistently across distributed enforcement nodes such as Prisma Access and Next-Generation Firewalls (NGFWs).
Without a shared inspection fabric, distributed enforcement quickly produces inconsistent security outcomes:
- Different threat detection quality in different locations
- Different interpretations of policy
- Different update cadences
- Different operational behaviours during incidents
Cloud-Delivered Security Services address this by ensuring that inspection logic, threat intelligence, and detection models are shared and continuously updated, regardless of where traffic is enforced.
Advanced Security Capabilities
Traditional security models often rely on point-in-time decisions. Cloud-Delivered Security Services evaluate traffic throughout the session, with updated threat intelligence and detection logic applied in real time. This means trust is continuously evaluated and not implicitly inherited.
In the platform context it's useful to think of CDSS as shared inspection services consumed by the data plane, rather than features tied to a specific product.
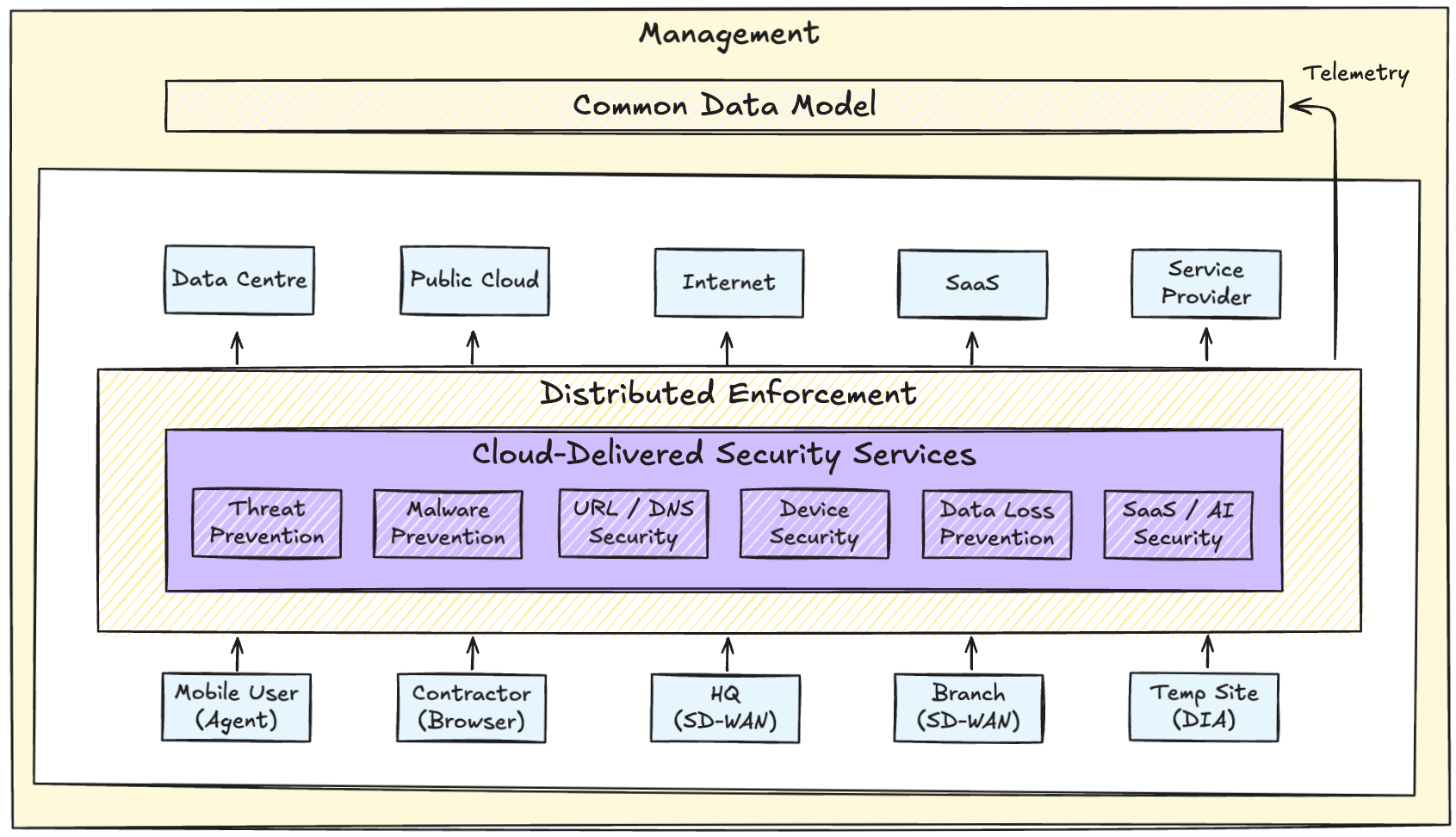
Examples of the types of capabilities delivered this way include:
- Threat prevention and intrusion detection
- Malware analysis and sandboxing
- URL filtering and DNS security
- IT and OT device security
- Content inspection and data loss prevention
- SaaS and AI detection and classification
The key point is not the individual capability - it's the shared capability layer. Overall visibility and intelligence is strengthened by context from other capabilities, and each control behaves the same way wherever traffic is coming from.
Precision AI
You'll increasingly see Precision AI referenced in Palo Alto documentation and marketing materials, and even on customer order forms. This can be confusing, particularly when we just established Cloud-Delivered Security Services as the platform layer for shared inspection and detection.
Precision AI is not a separate product or something you turn on independently. When a customer licenses Cloud-Delivered Security Services, the security capabilities they consume are powered by Precision AI under the hood. The naming reflects the method, not a new architectural layer.
Precision AI describes how inspection, classification, and threat detection are performed using machine learning and deep learning models trained on large-scale telemetry.
Telemetry from real-world enforcement continuously feeds detection models, creating a feedback loop that improves inspection quality across the entire platform.
The need for AI-driven inspection is becoming foundational to effective security operations. As traffic becomes encrypted and application-centric, behavioural and contextual analysis is required to identify threats that evade traditional signature and port-based inspection models.
Single-Pass Architecture
Precision AI is designed to operate within a single-pass inspection architecture. At a very high level this means:
Traffic is decrypted once, inspected once, and evaluated against multiple security controls in parallel.
With traditional security tooling, teams are forced to compromise on security services by applying controls selectively for performance and licensing. Separate engines (firewall, IPS, malware, DLP, URL filtering) are chained together which directly impacts performance, latency, and operational complexity.
The single-pass inspection is not just an implementation detail - it's one of the reasons a platform approach scales. Remember the Cloud-Delivered Security Services (with single-pass architecture as an enabler) are consumed by the data plane, and not something operators deploy (although they do define policy).
Operational Outcomes
When the services discussed are applied as part of a NetSec platform, the outcomes are tangible:
- Consistent security controls across locations
- Improved visibility and higher confidence in security posture
- Faster response to emerging threats
- Reduced policy and operational drift
- Lower operational overhead
