NetSec Platform: Prisma Access (Distributed Enforcement Architecture)
In the previous post, I described Prisma Access as the distributed enforcement layer within the NetSec platform - steering user and branch traffic into regional enforcement points under a unified control plane.
If you are new to the discussion, it is worth reviewing that post before continuing. This article builds on those foundations and examines how the enforcement fabric itself is constructed.
Distributed Enforcement
Prisma Access is a a composition of enforcement nodes, routing domains, and service insertion points. Traffic enters the enforcement fabric through regional locations. Traffic inspection and enforcement is carried out at compute locations, by the appropriate Security-Processing Node (SPN).
Customer traffic is isolated within its own tenant and dedicated SPNs, preserving logical separation within the shared service infrastructure.
The distributed enforcement fabric comprises distinct attachment points and processing roles, each optimised for specific traffic domains:
Mobile-User Security-Processing Nodes (MU-SPN) - enforcement nodes optimised for identity-driven user traffic
The MU-SPN mapping and agent configuration is managed by Portal Nodes
Explicit-Proxy Security-Processing Nodes (EP-SPN) - enforcement nodes for explicit proxy-based web traffic
Remote-Network Security-Processing Nodes (RN-SPN) - enforcement nodes optimised for site-originated traffic
Service-Connection Corporate-Access Nodes (SC-CAN) - controlled ingress/egress boundaries for layer 3 private connectivity
ZTNA Tunnel Terminators (ZTT) - termination points for outbound-initiated layer 7 application connectors
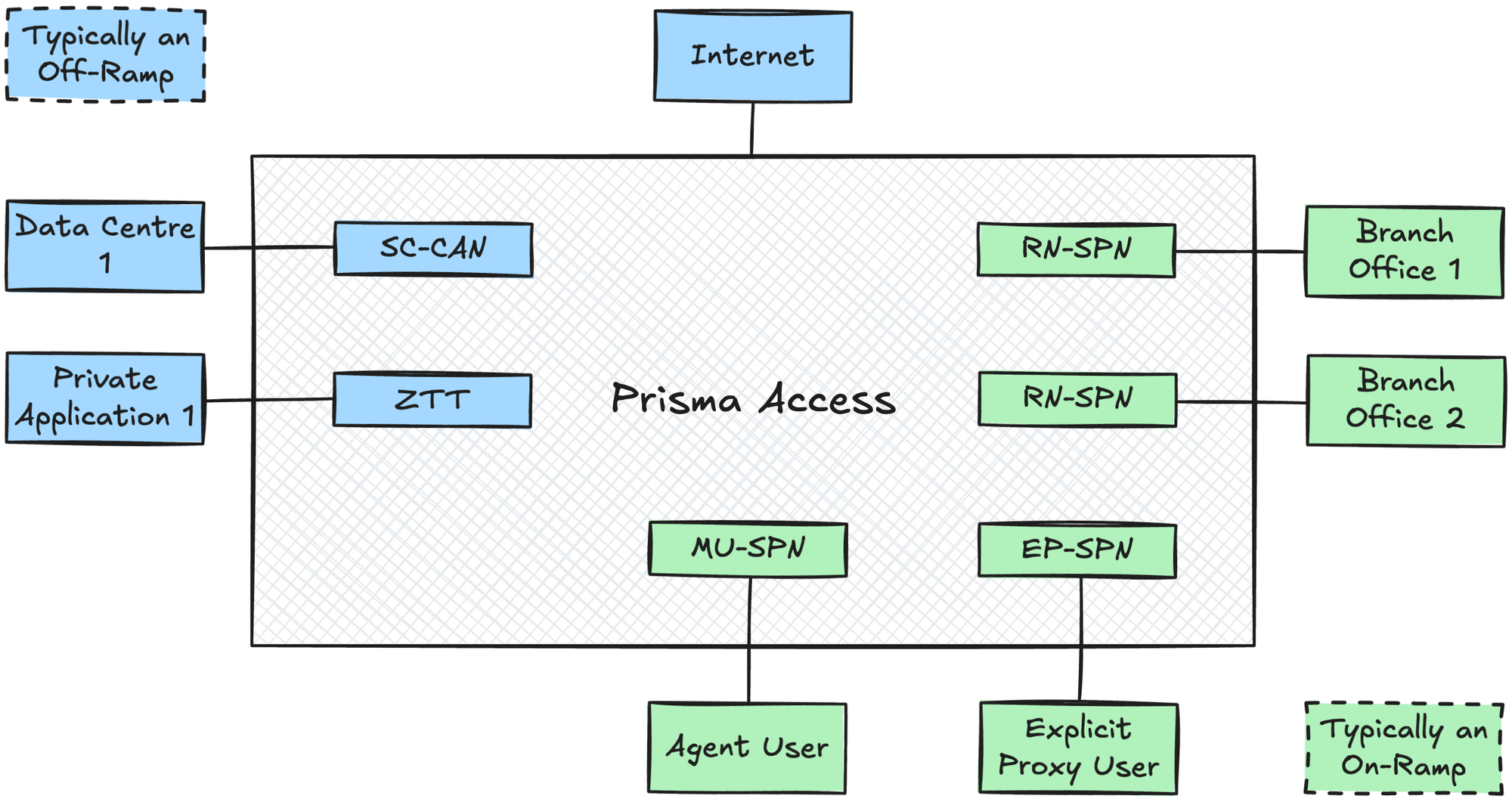
Internally, the enforcement fabric uses iBGP for node-to-node routing with a customer-defined service infrastructure subnet.
Where Customer Premises Equipment (CPE) is connected (Remote Networks or Service Connections), eBGP is used.
Organisations may deploy one or multiple attachment types depending on the scale and complexity of their environment.
Control Plane
Strata Cloud Manager (SCM) is used for Prisma Access deployment and operations.
Administrators specify the desired configuration and automated workflows provision the underlying infrastructure. All cloud nodes operate under a unified control plane.
Security policy is:
- Defined once in SCM
- Distributed consistently to SPNs across regions
- Executed locally at each enforcement node
- Logged and correlated centrally for visibility and analytics
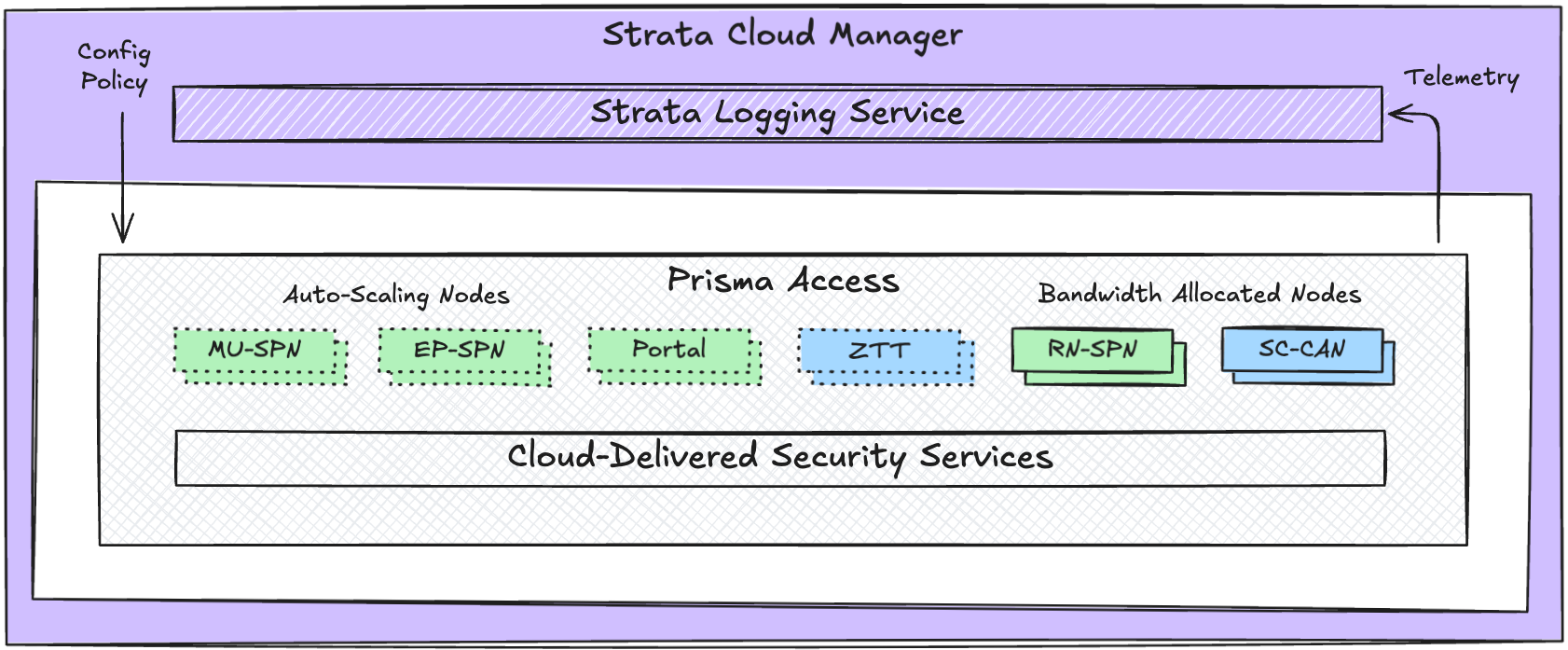
We know from previous posts that Strata Cloud Manager provides unified management for the network security platform, with Strata Logging Service (SLS) normalising telemetry into a common data model.
Cloud Identity Engine (CIE) obtains user, group, and authentication data from external identity providers. CIE enables Prisma Access to use identity-based controls rather than relying on traditional IP address-based policies.
Shared Responsibility
Because Prisma Access is delivered as a managed service, the distributed enforcement fabric is maintained and operated by Palo Alto rather than deployed as customer-owned appliances.
This includes the underlying service infrastructure that connects regional ingress and compute locations, as well as the orchestration systems that provision and scale enforcement components.
Customers do not deploy or manage individual appliances. They define policy in the control plane and onboard users, locations, and applications.
Provider Responsibilities:
- Regional infrastructure lifecycle
- Maintaining inspection engines and content
- Capacity scaling and elasticity
- High availability design
- Platform upgrades and patching
- Core service integrity
- Securing the underlying cloud platform
Customer Responsibilities:
- Defining and maintaining security policy
- Onboarding users, branches, and private connectivity
- Design of access patterns and application segmentation
- Identity integration
- Monitoring and responding to security events
Governance and policy authority remain with the customer, while operational responsibility for the infrastructure shifts to Palo Alto Networks.
Remember that Prisma Access is not a collection of independent nodes. It is a coordinated enforcement fabric operating across regions, governed centrally and executed locally.
Users, branches, and private applications all attach to the same distributed system. Policy is defined once and enforcement is applied consistently. This approach enables scale without fragmenting security.
