NetSec Platform: Prisma Access
At a high level, Prisma Access is a distributed security enforcement layer. The key concept is that security enforcement happens in a cloud-delivered security edge, close to users and applications, rather than a single physical location (like a data centre firewall).
Prisma Access provides consistent controls for:
- Remote users
- Branch and site connectivity
- Internet and SaaS access
- Private application access
In industry language Prisma Access is a Security Service Edge (SSE). It can be combined with native SD-WAN to form a Secure Access Service Edge (SASE).
In platform language Prisma Access forms a major part of your data plane, with central policy management from Strata Cloud Manager (SCM) creating the control plane.
Prisma Access Use Cases
Most organisations adopt Prisma Access for one of 3 reasons:
Use case 1: Remote work. We know traditional VPN and data centre inspection don't work when the majority of traffic is internet and SaaS bound, users are distributed and mobile, and performance expectations are high.
Platform outcome: remote access becomes standardised, least privilege by design, and easier to audit and troubleshoot. Users get fast, direct-to-app connectivity with full security inspection.
Use case 2: Branch transformation. Branch estates have grown organically and are difficult to operate with different firewall models and versions, local policy standards, and inconsistent visibility.
Platform outcome: branch security and policy becomes repeatable, automated, and consistent across locations. Legacy WAN and branch firewall models can be simplified or replaced when combined with SD-WAN.
Use case 3: Zero Trust. Prisma Access provides Zero Trust Network Access (ZTNA) 2.0 which continuously verifies identity and device posture after a connection is established. This aligns with Zero Trust principles such as the Kipling method, where access decisions are based on who, what, where, when, why, and how - not network location.
Platform outcome: users can only reach the specific applications they need, significantly reducing the blast radius of a potential breach. Access is given to private applications without extending the full corporate network.
Access Patterns
Prisma Access has a cloud-delivered operating model, so the core components are consumed as a service. That means you don't need to deploy and maintain security gateways or other infrastructure components.
From a platform design perspective, the key point is:
Prisma Access acts as a central enforcement layer that your users, sites, and environments connect into. Traffic is then inspected and controlled according to policy before it reaches its destination (internet, SaaS, public cloud, or private applications).
This hosting model changes the traditional perimeter design in 2 important ways:
1) Enforcement moves closer to the natural traffic path (especially for internet and SaaS), reducing reliance on backhauling everything through a central data centre.
2) Security becomes a service edge, which provides standardisation and scale across remote users and sites, rather than being tied to a single physical location.
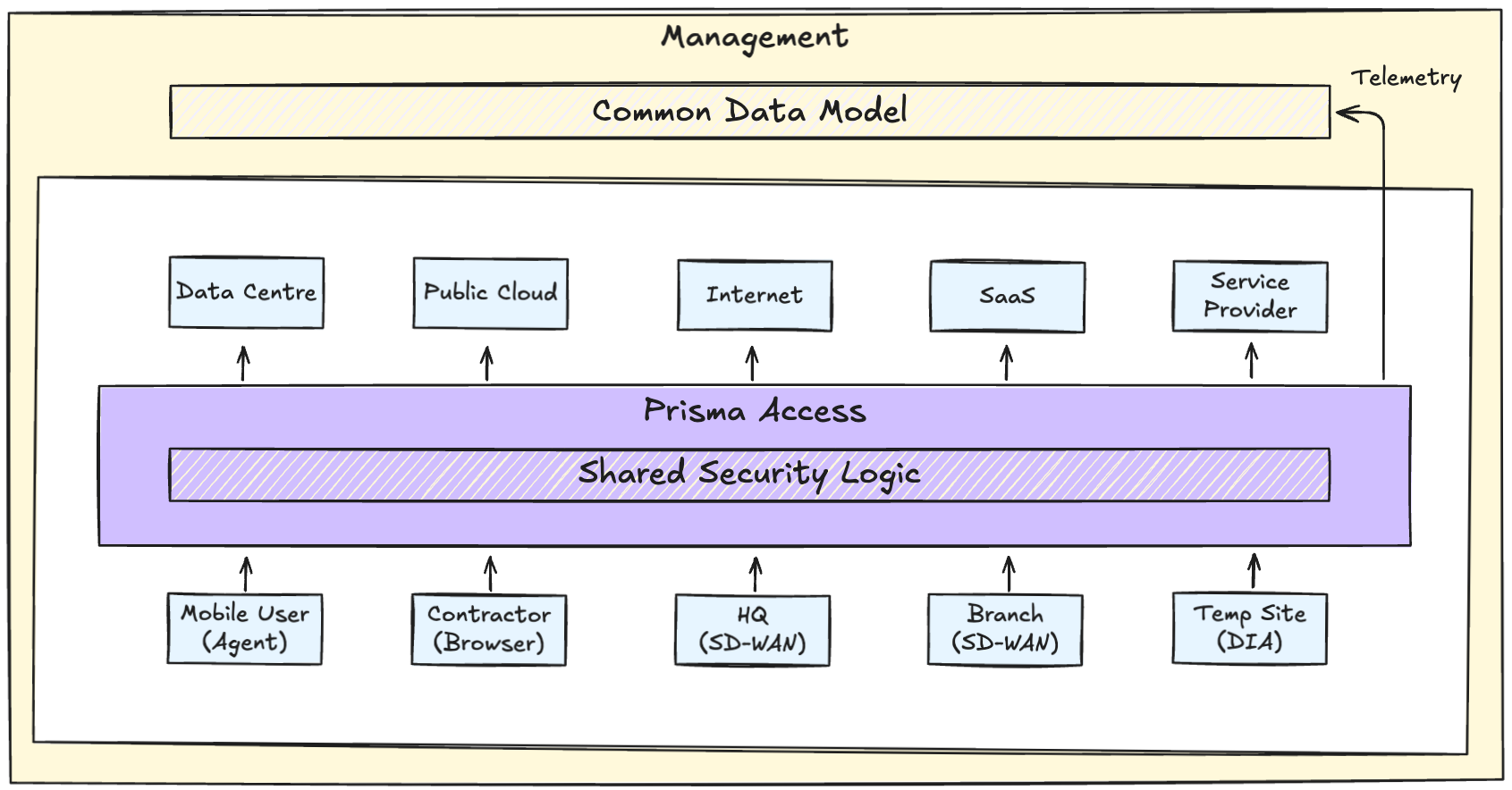
Prisma Access provides multiple on-ramp and off-ramp patterns that define how traffic enters and exits the enforcement fabric.
On-ramps:
- Mobile Users: supports multiple methods including agent-based, explicit proxy, portal, or secure browser
- Remote Networks: connects branch offices via standard IPSec or SD-WAN
Remote Networks can also act as an off-ramp for users needing to access services hosted locally within a branch
Off-ramps:
- Internet: direct, secure egress through the Prisma Access backbone
- Private Applications:
- Service Connection: a network-centric off-ramp, which also functions as an on-ramp for infrastructure traffic
- Zero Trust Network Access (ZTNA) Connector: an application-centric off-ramp
Private Interconnects:
These options provide private, high-bandwidth, low-latency connectivity into the Prisma Access fabric, avoiding public internet transit. They are typically used in large-scale or service provider environments.
- Service Provider Interconnect: direct backbone interconnect allowing an Internet Service Provider (ISP) to natively connect into the Prisma Access fabric with VLAN-based hand-off
This enables ISPs to deliver Clean Pipe services, where traffic is inspected and scrubbed before reaching downstream networks - Private Connect: Cloud Interconnect: privately connects public cloud Virtual Private Clouds (VPCs) or Virtual Networks (VNETs) directly into the Prisma Access fabric
- Private Connect: Colo Connect: privately connects infrastructure hosted in third-party colocation facilities into the Prisma Access fabric
The patterns described above are often combined in real-world environments, rather than used in isolation.
The common thread across all access types is that rather than relying on a one-time trust decision, enforcement and inspection are applied continuously through the session.
Platformise for Success
There isn't a one size fits all deployment for Prisma Access. The core idea stays consistent - traffic is steered into a cloud-delivered enforcement layer - but the design choices and operational outcomes change depending on the use cases you're prioritising.
As with any distributed enforcement model, resilience and degraded-mode behaviour should be intentionally designed rather than assumed.
Across all use cases, successful deployments share the same mindset:
- Prisma Access is an enforcement layer
- Identity and policy structure are designed intentionally
- Connectivity and routing are treated as security architecture
- Visibility and operations are planned from day 1
It's important to be clear about what makes the outcome a platform, rather than simply a cloud security service.
A NetSec platform isn't defined by where enforcement happens. It's built with a common policy model, common visibility, and common security controls that scale consistently.
Prisma Access, Strata Cloud Manager, and the Cloud-Delivered Security Services are different layers of the same Palo Alto NetSec platform:
Prisma Access: distributed enforcement layer
Strata Cloud Manager (SCM): common policy, visibility, and management
Cloud-Delivered Security Services (CDSS): shared security inspection and controls
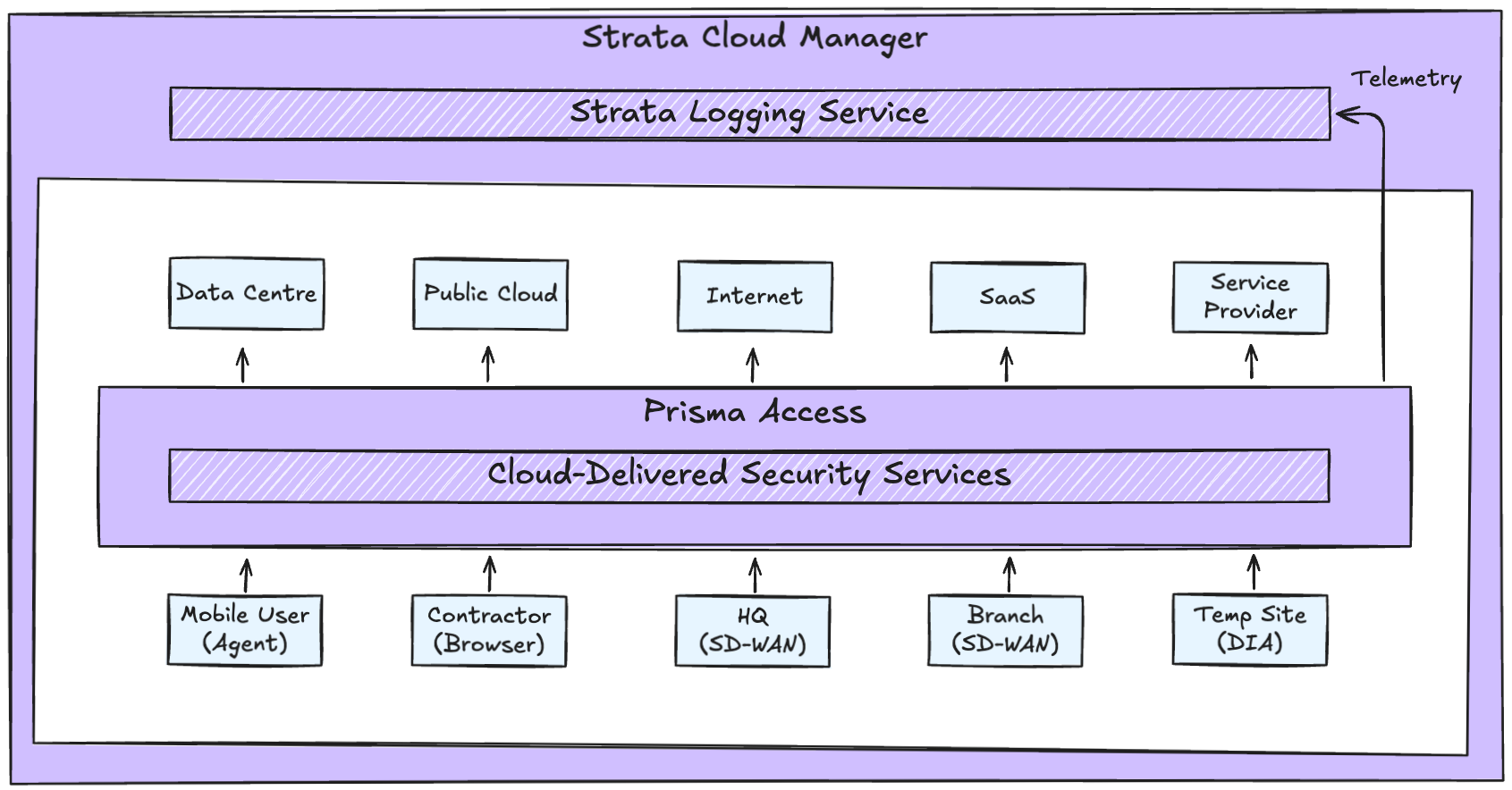
Together, these layers form a deliberate system that's consistent, observable, and scalable. This delivers the platform outcome.
