NetSec Platform: Strata Cloud Manager (SCM)
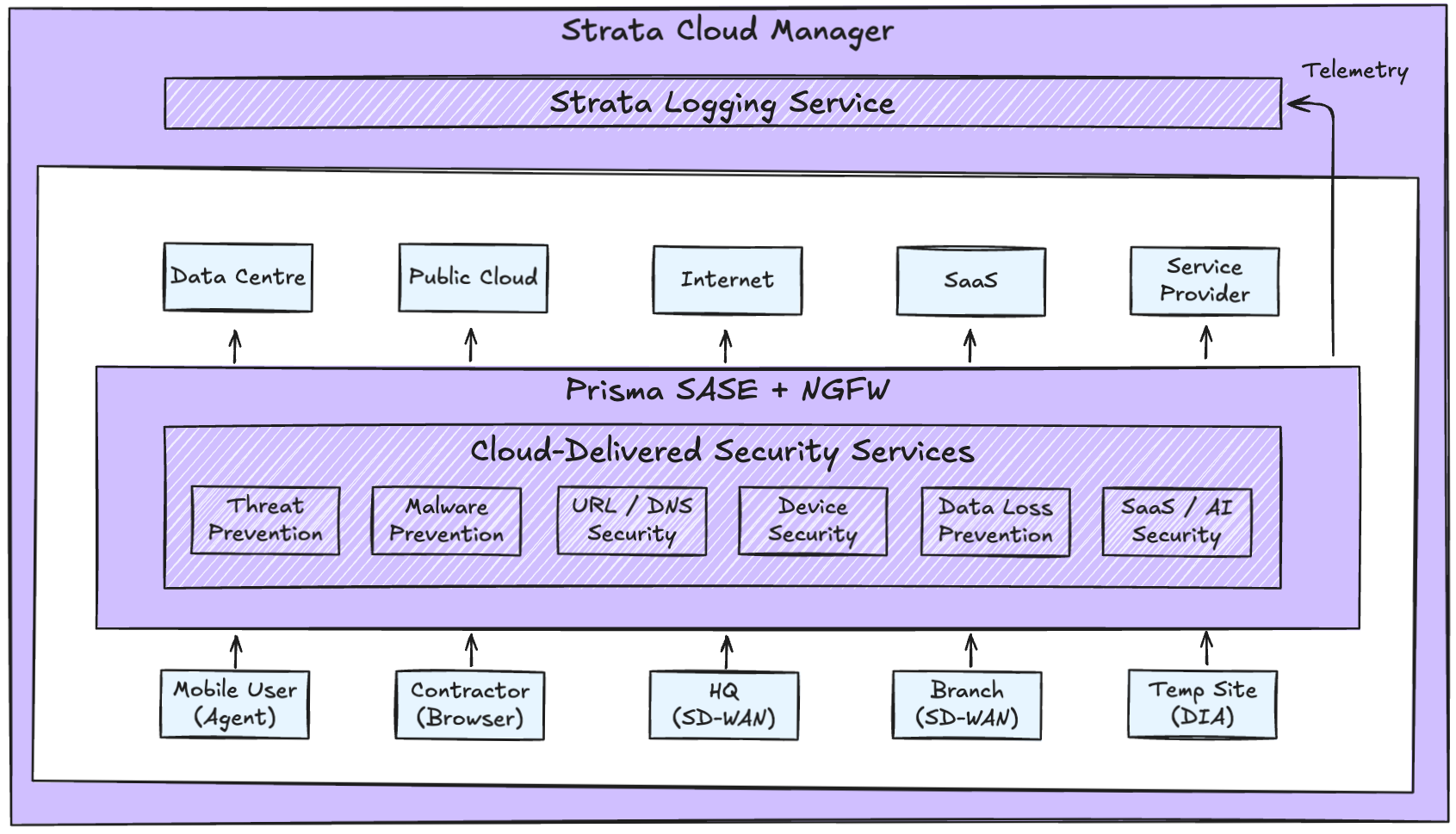
The NetSec platform reference model defines 3 layers: management, inspection, and enforcement. These layers must operate as a coherent system rather than as independent components.
This post focuses on the management layer – the control plane responsible for policy, visibility, and operational workflows.
Most organisations already operate security across multiple domains - remote access, data centre, cloud, SaaS, internet edge, and endpoint. The issue is not capability coverage. The issue is fragmentation.
Policy, telemetry, and operations are typically distributed across separate tools and teams. No single system has authoritative visibility or control.
SCM as the Control Plane
Traditional network security management evolved around appliances. Each service operated as its own configuration and telemetry domain.
In a distributed enforcement architecture, policy authority must be abstracted from individual devices. Strata Cloud Manager (SCM) provides that abstraction.
SCM is a cloud-delivered management and visibility layer for the Palo Alto NetSec platform. It is the anchor point that makes the rest of the system consistent and observable.
Architecturally, it functions as the control plane to:
- Define and distribute policy
- Normalise telemetry across enforcement form factors
- Provide lifecycle management and configuration governance
- Centralise operational workflows and analytics
SCM maintains a hierarchical model where global policy, shared objects, and service-specific rules are defined centrally and applied consistently across the platform.
SCM leverages Strata Logging Service (SLS), which normalises telemetry from different enforcement form factors into a common data model.
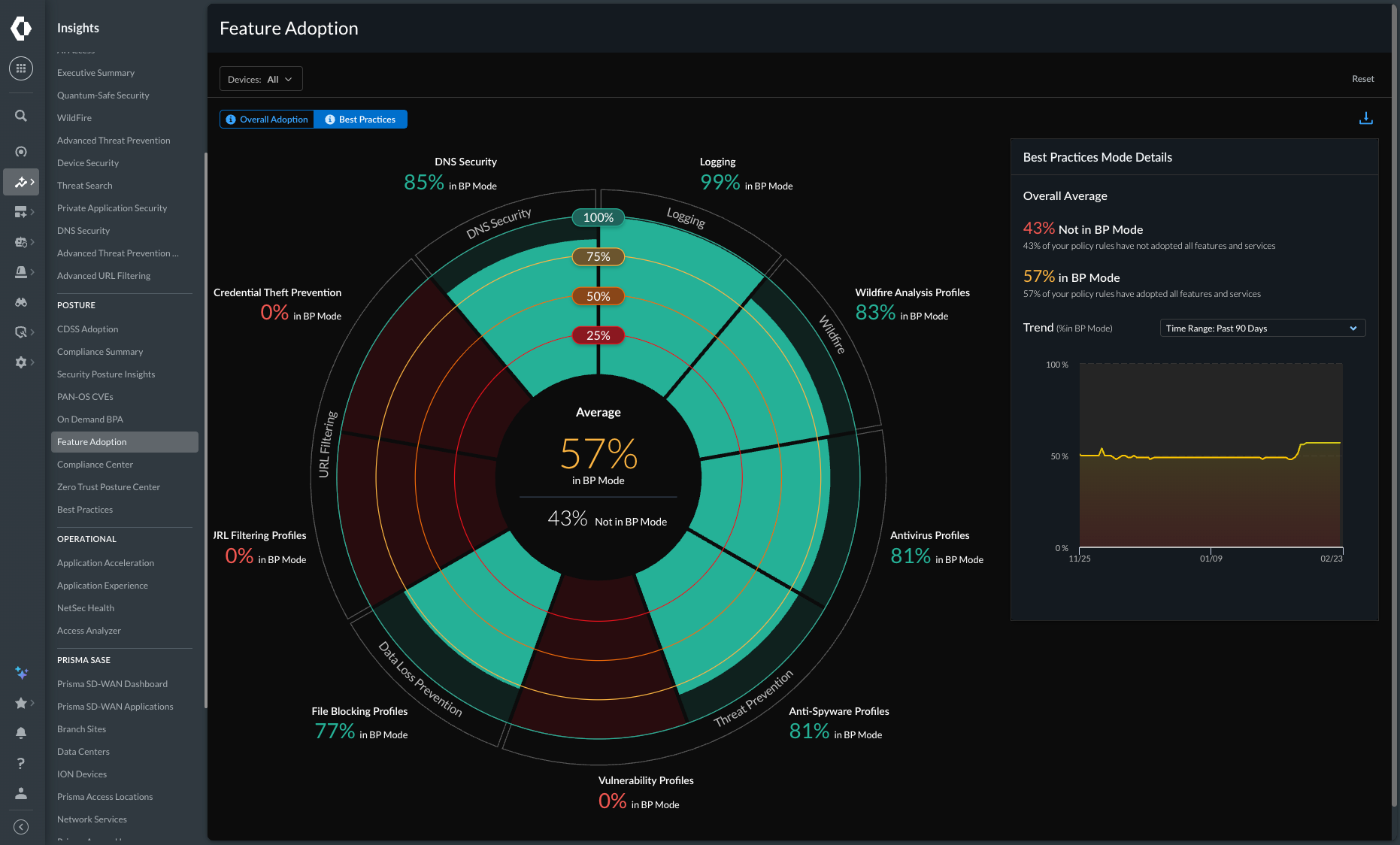
On top of this unified data model, SCM applies analytics and deep learning to surface contextual insights, policy recommendations, and operational guidance.
Enforcement remains distributed across firewalls and cloud-delivered services; policy authority and logging are centralised.

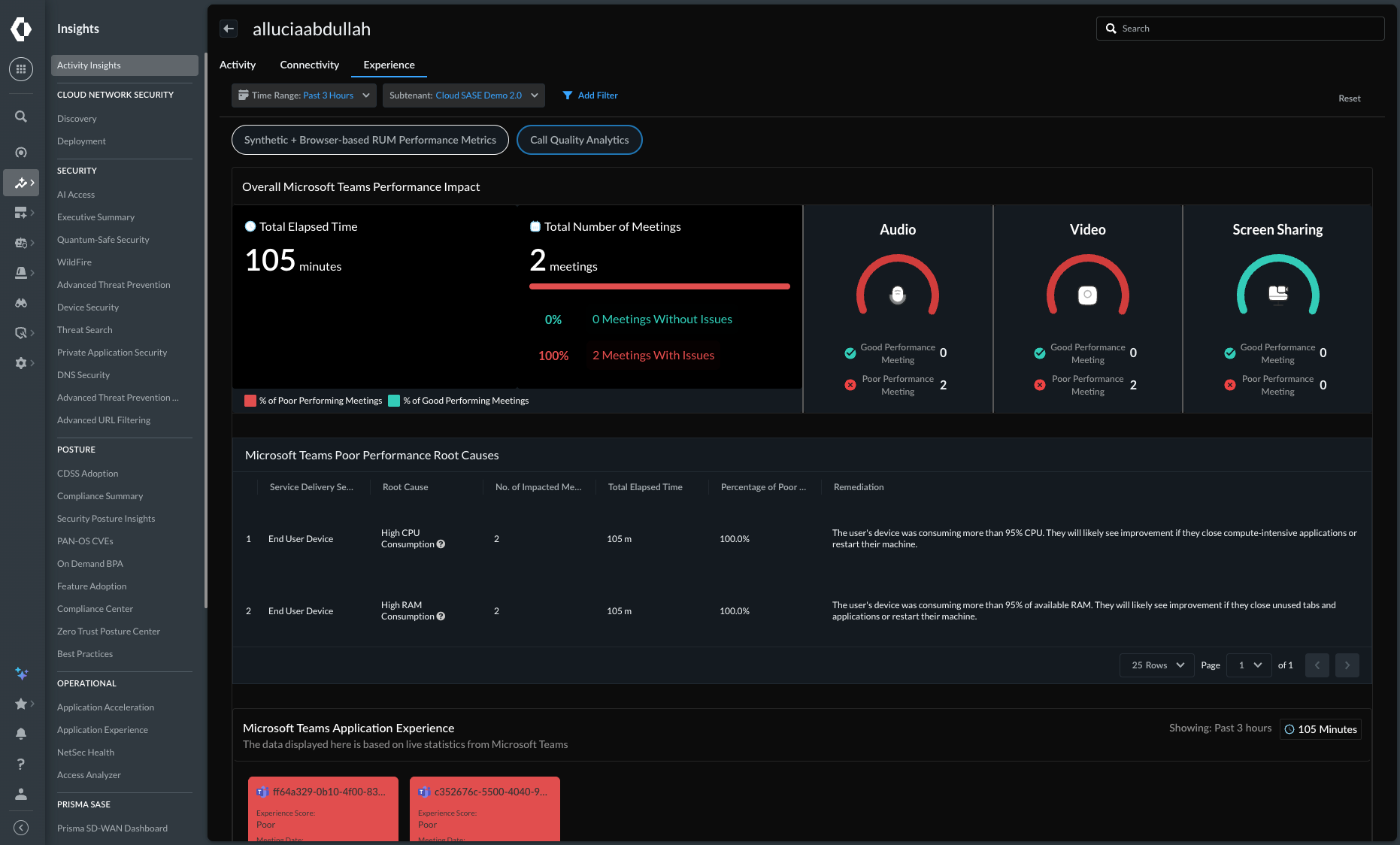
Example Platform Outcome: ADEM
Autonomous Digital Experience Management (ADEM) is an observability and experience management solution delivered through SCM.
ADEM would not be possible in a fragmented architecture. It depends on policy context, enforcement telemetry, and endpoint signals existing within the same control plane.
It uses machine learning to identify issues and determine root cause across multiple domains:
- End-to-end segment monitoring (RUM, synthetic testing)
- Endpoint telemetry (CPU, memory, WiFi)
- First and last mile metrics (LAN, ISP)
- Security service telemetry (Prisma Access, NGFW)
- Application performance metrics (latency, connection time)
ADEM calculates a health score for every user, site, and application. It can alert IT, generate a ticket, or provide automated self-service guidance to users.
This reduces help desk volume, manual investigation, and Mean Time to Resolve (MTTR).
Operational Scenario
Scenario: User reports "Teams is slow."
Without SCM:
- Check endpoint
- Check remote access solution
- Check firewall logs
- Check ISP metrics
- Check SaaS application portal
With SCM:
- Single user view
- Health score with domain breakdown
- Correlated enforcement, endpoint, and network telemetry
- Suggested root cause

Operational Considerations
From a deployment and operations perspective:
- SCM Essentials is included with relevant Palo Alto products
- SCM Pro enables broader platform-level operational capabilities
- There is a migration tool available for existing Panorama users
- Cloud-delivered services are hosted on hyperscale infrastructure
- Region selection on deployment (e.g. UK) ensures compliance with data residency requirements
When management, visibility, and enforcement are unified under a single control plane, operational complexity decreases.
Policy can be defined once and applied consistently across environments. Telemetry becomes contextual rather than siloed. Troubleshooting shifts from device-level inspection to system-wide correlation.
In a NetSec platform model:
- Enforcement scales horizontally
- Inspection capabilities are shared
- Management operates as a central authority
The control plane prevents operational sprawl. This is the difference between "we deployed a service edge" and "we built a security platform".
