NetSec Platform: Zero Trust
Zero Trust is an approach to network security that removes implicit or assumed trust. It isn't a product and it isn't owned by any one vendor.
At a high level, Zero Trust is built on a simple idea:
Never trust by default, always verify. Apply least privilege access, and assume breach.
In practical NetSec terms, Zero Trust means:
- Access is explicitly granted (not assumed)
- Identity context is central (user, device, application)
- Trust is dynamic (it can change mid-session)
- Security inspection is continuous (visibility is mandatory)
- Controls are enforced consistently (regardless of location)
Zero Trust doesn't mean you treat every connection as hostile. It means trust is earned and verified, rather than inherited just because a user is on the corporate network.
Why Does Zero Trust Matter?
Traditional network security was built around a perimeter mindset, placing the firewall as the boundary with Virtual Private Network (VPN) extending the trusted network outward. It assumed everything inside the network was trusted (implicit trust) and everything outside the network was untrusted.
That model no longer scales safely in modern environments. Users and applications are distributed and trusted networks now contain more unmanaged connected devices and third parties than ever before. Lateral movement has become a primary attack path.
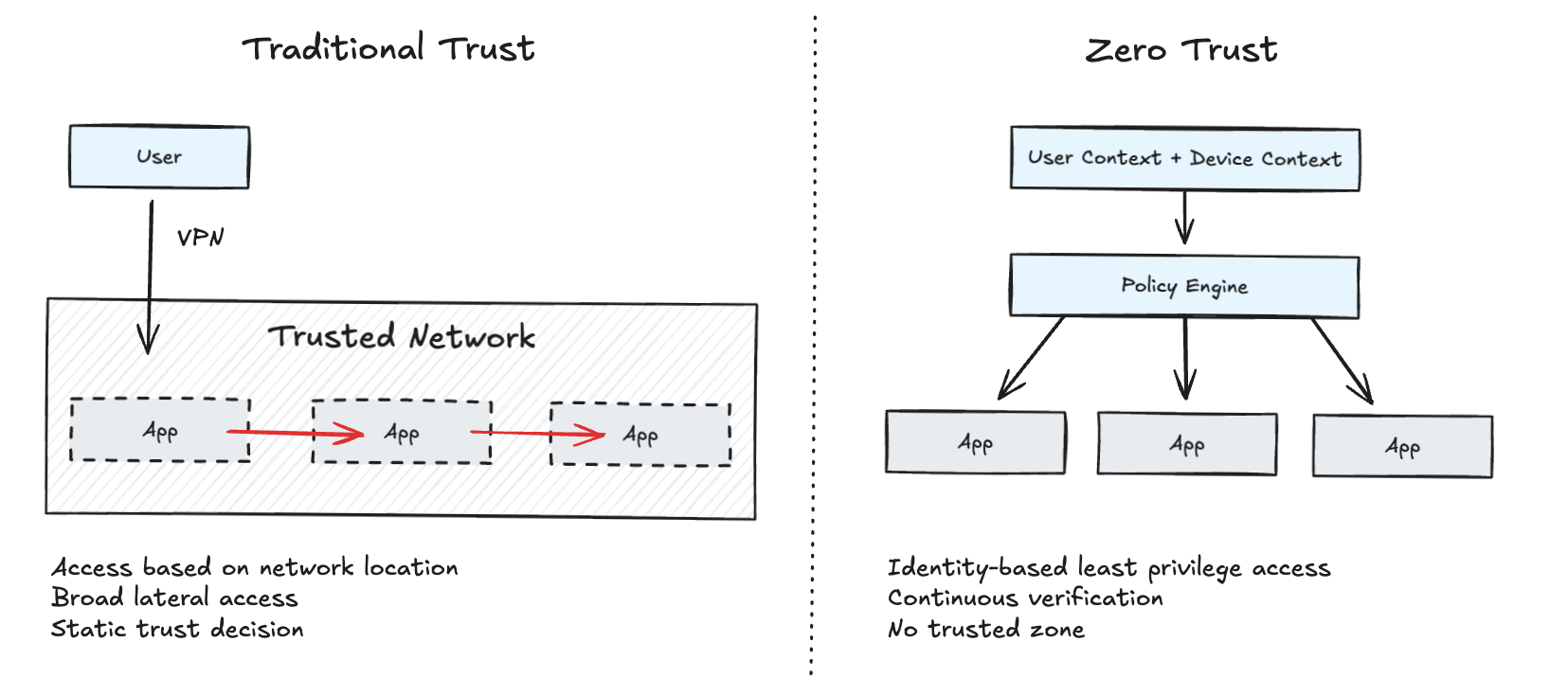
Zero Trust as a platform outcome is created by combining:
- Identity and device context
- A policy engine that can clearly express intent
- Distributed enforcement points
- Predictable connectivity and traffic steering
- Visibility and operations
If that sounds familiar, it should - it maps directly to the NetSec platform building blocks from my earlier posts.
The Kipling Method
The Kipling Method is a simple way to structure security policy decisions that reflect the business outcomes you want:
- Who is the user?
- What is the application?
- Where is the user/device?
- When is the access happening?
- Why is the access needed?
- How is the access being made?
Together, these questions ensure access decisions are intentional, explainable, and auditable.
How Palo Alto Networks Enables Zero Trust
Taking a broader platform approach can ensure Zero Trust principles are applied consistently, using identity and context as first-class policy inputs.
Palo Alto's Zero Trust approach is heavily enabled by a set of identification and context capabilities. They allow you to enforce policy based on real context rather than network assumptions.
Each of the items below is a platform capability (policy inputs and enforcement functions). They appear across multiple Palo Alto form factors such as Prisma Access, Next-Gen Firewall (NGFW), and other cloud-delivered services. They are not standalone products you license individually.
User-ID: maps network activity to a user identity (and group membership). It replaces source-IP trust with identity-based decisions.
App-ID: identifies applications at Layer 7. It replaces port-based policies with enforcement based on the actual application and actions within it.
Device-ID: helps distinguish managed vs unmanaged devices and provides device context for policy decisions. It is typically combined with User-ID for comprehensive decision making.
Content-ID: covers capabilities like content inspection and data controls. Zero Trust isn't only about who is connecting to what, but also what can they do and what data can they move. This is especially important for SaaS and AI-driven applications.
Honourable mention for policy-based decryption: most traffic is encrypted and that's naturally where threats will reside. If you can't see it you can't verify it, which stops policy being enforced consistently.
Putting this together, a Zero Trust policy in practice becomes something like:
- Allow the right users
- on the right devices
- to access the right applications
- using the right methods
- with continuous inspection and visibility
- and enforce least privilege by default
This is a meaningful shift from:
"Allow traffic from subnet A to subnet B on ports 443 and 22"
to:
"Allow engineering users on compliant devices to access approved developer applications, with logging, MFA, and threat prevention enabled."
Operational Outcomes
The goal of Zero Trust isn't to make access harder - it's to make access safer, more consistent, and easier to operate at scale. Here is what good looks like:
Consistent access decisions and reduced gaps: users get a predictable experience and the same security outcome whether they are in the office, at home, or travelling.
Smaller blast radius and reduced lateral movement: if an account or endpoint is compromised, the attacker should not automatically gain broad internal reach.
Stronger security posture and reduced manual work: Zero Trust shifts security from one-off network design decisions to repeatable policy enforcement. Cleaner policies based on users, groups, devices, and applications scale well over time.
Improved visibility and faster troubleshooting: when enforcement decisions are tied to identity and application context, it becomes easier to understand why access was allowed or denied.
