NetSec Spotlight: Data Loss Prevention (DLP)
Data Loss Prevention (DLP) is a core network security capability focused on identifying sensitive information and enforcing policy to prevent exposure.
This post examines the role of DLP within the NetSec platform, and how content-aware inspection enables consistent protection across the modern workforce.
As organisations increasingly adopt AI-powered tools, the same data protection principles used in DLP become increasingly relevant to governing AI-driven interactions. In a subsequent post, we will introduce AI Access Security as a specialised capability that applies content-aware controls to AI prompts, responses, and data flows, incorporating AI-specific context and risk.
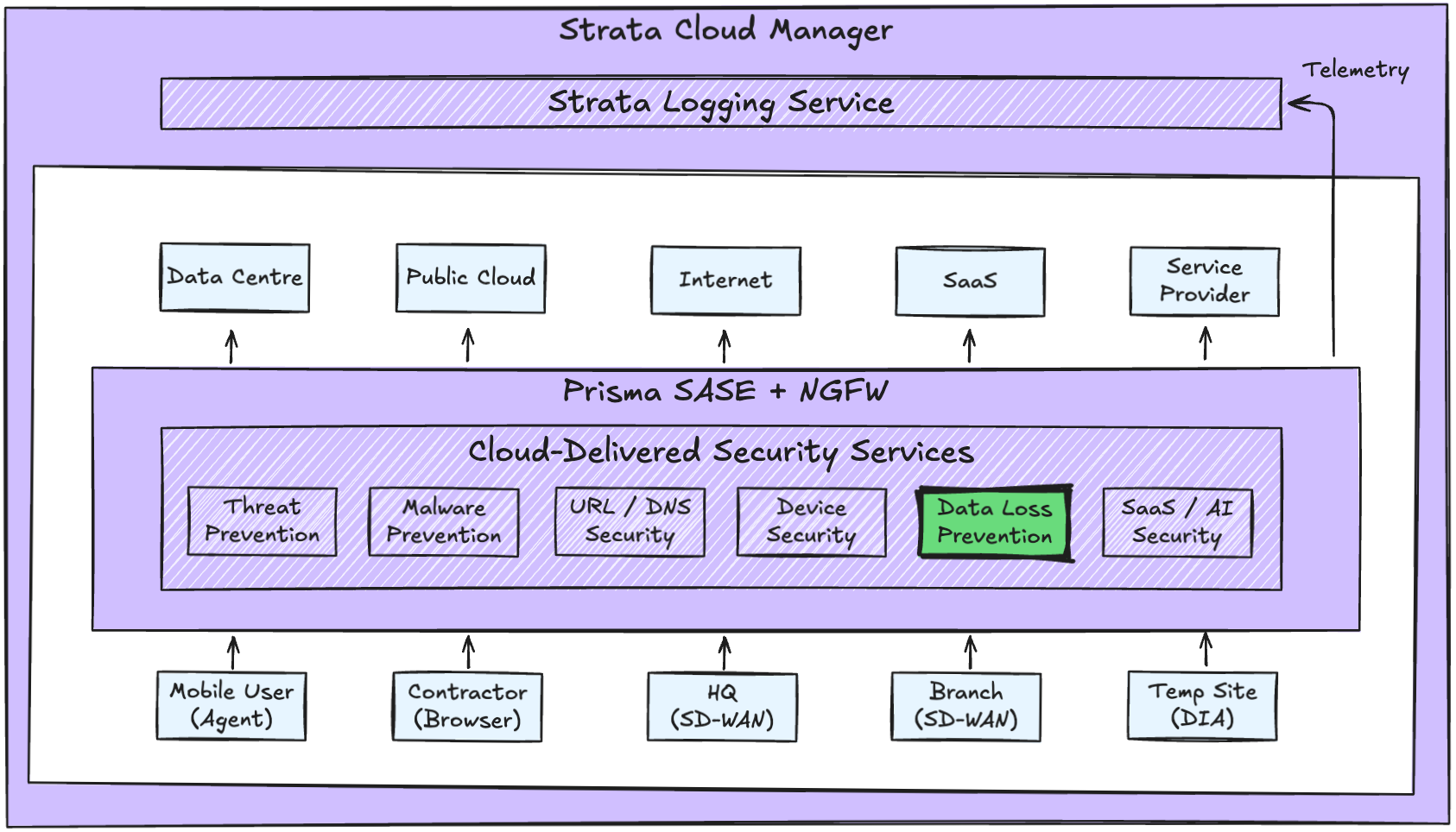
Platform Context
In many environments, DLP is implemented as a separate proxy, gateway, or endpoint-only control, or reduced to a compliance-driven reporting tool.
This leads to predictable issues:
- Inconsistent inspection coverage
- Gaps between network, SaaS, and remote access controls
- Multiple policy engines defining sensitive data differently
- Fragmented logging and investigation workflows
Within the NetSec platform, DLP is a shared inspection capability delivered through Cloud-Delivered Security Services and governed centrally.
Architecturally:
- Policy authority remains centralised
- Enforcement remains distributed
- Inspection is applied inline and continuously
- Telemetry is normalised within the same data model
DLP operates as part of the same single-pass inspection pipeline that evaluates application, user, device, and threat context.
Because DLP is embedded directly in the inspection layer:
- Traffic is decrypted once
- Content inspection occurs inline
- DLP policies are evaluated in parallel with other controls
- Enforcement decisions are applied immediately
There is no service chaining or redirection to an external inspection tier.
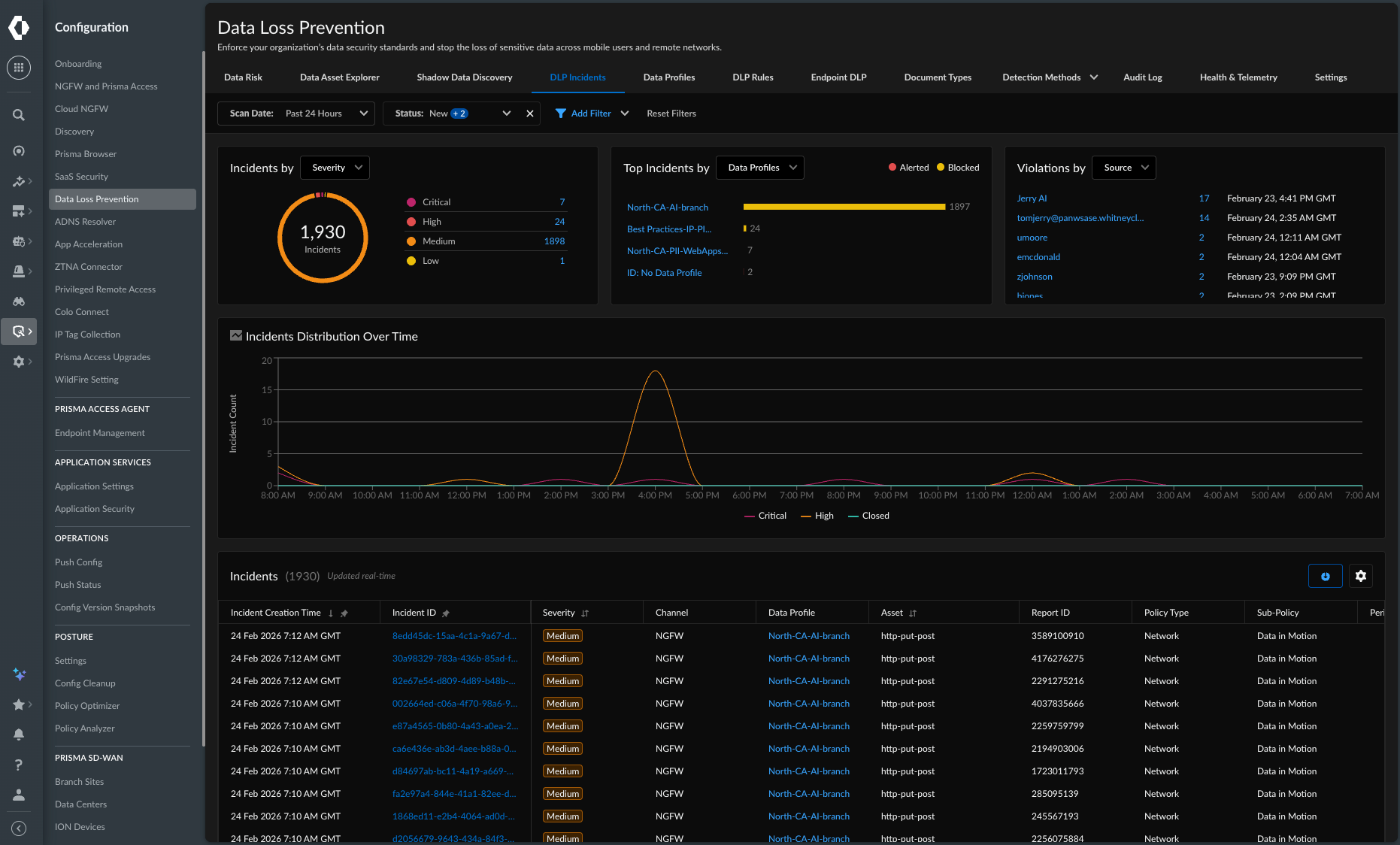
Operational Capabilities
DLP does not operate in isolation. It evaluates data exposure in the context of user identity, device posture, application risk, and access method.
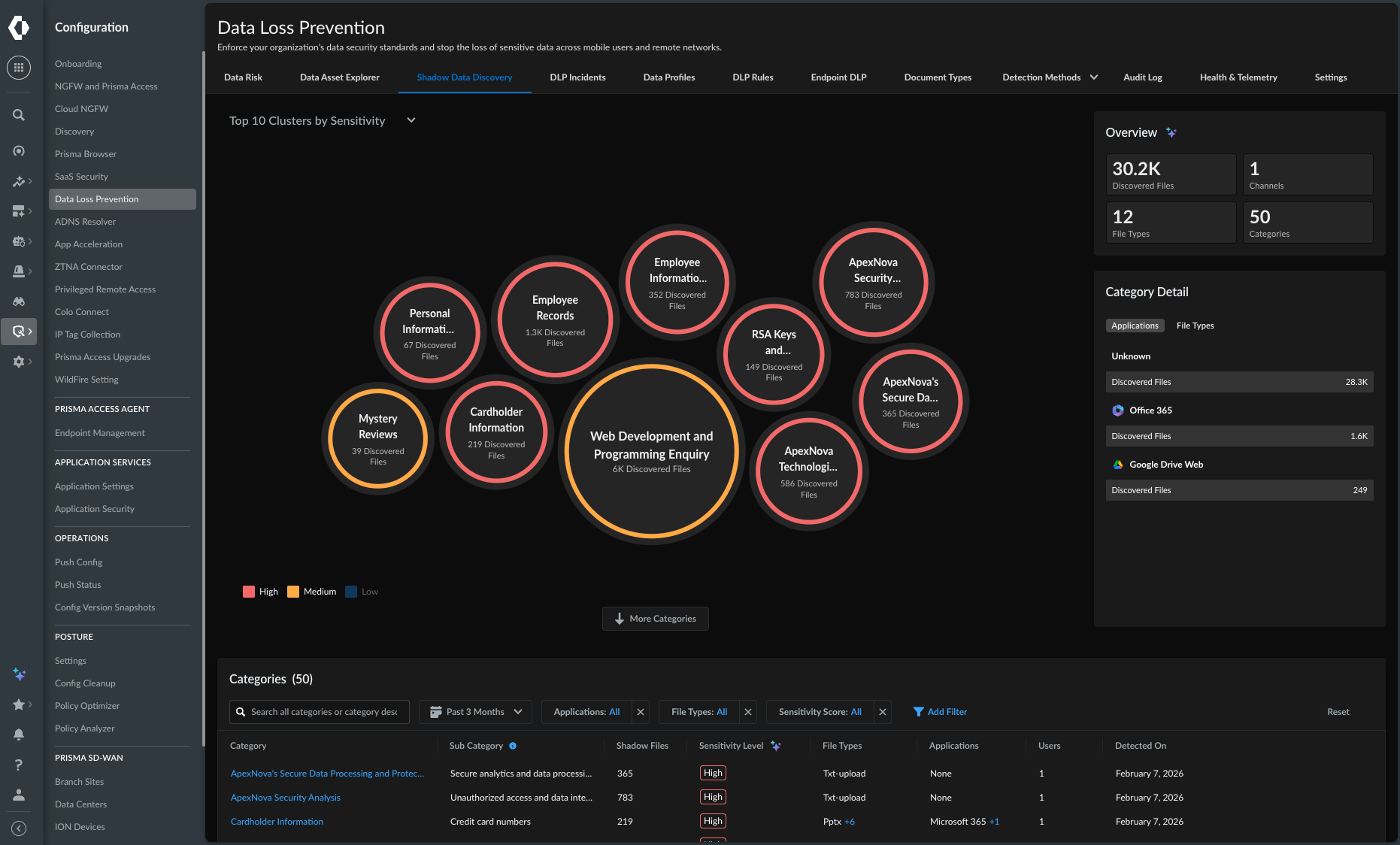
Within the platform, DLP provides:
- Inline inspection of data in motion
- Endpoint inspection of data at rest and in use
- Inspection of SaaS application data, including inline user interactions and data at rest
- Optional last-mile data protection via secure browser
- Consistent classification of sensitive data types
- Context-aware policy enforcement
- Unified logging and alerting
Sensitive data is identified using multiple inspection techniques applied inline as part of the platform inspection pipeline. Structured data formats, keywords, and pattern matching are combined with machine learning-based classification to recognise sensitive information even when it does not follow fixed or predictable patterns.
This approach improves accuracy and reduces false positives compared to pattern matching alone. Data classification can be tuned over time by refining models with organisation-specific content to improve detection.
Because DLP is governed through the same policy hierarchy as other NetSec controls, organisations can enforce granular outcomes, including:
- Allowing access while blocking uploads of sensitive data
- Restricting data exfiltration to unsanctioned destinations
- Applying stricter controls based on user role or device posture
- Enforcing different policies for internet, SaaS, and private applications
Policy intent is defined once and applied consistently across enforcement points.
Operational Scenario
Scenario: User uploads a document containing sensitive data to a personal file-sharing service.
Without platform DLP:
- Application identified
- Traffic decrypted and inspected inline
- No content-aware data inspection
- Data exposure undetected
With platform DLP:
- Application identified
- Traffic decrypted and inspected inline
- Sensitive data detected
- DLP policy evaluated in context
- Upload blocked or restricted according to policy
No additional tools or workflows are required.
Platform Outcomes
When DLP is implemented as part of a NetSec platform, the outcomes include:
- Consistent data protection across all access patterns
- Reduced reliance on fragmented point solutions
- Lower operational overhead for security teams
- Improved confidence in inspection coverage
- Policies that adapt as applications and usage evolve
Most importantly, data protection becomes predictable and enforceable at scale.
