NetSec Spotlight: Cloud NGFW
Cloud adoption has fundamentally changed how network security needs to be delivered. Traditional firewall models, built around fixed perimeters and static network boundaries, don't translate cleanly into environments where workloads are ephemeral, distributed, and even span multiple cloud providers.
In cloud environments:
- Workloads are dynamic and short-lived
- East-west traffic exceeds north-south traffic
- Identity and metadata are more reliable than IP addressing
- Security boundaries are defined in software, not physical topology
However, there is a gap between cloud-native network constructs (VPCs, subnets, security groups) and the depth of inspection and control required for enterprise security.
Cloud NGFW addresses this by bringing consistent context-aware security controls into cloud environments, without legacy assumptions about network location or trusted zones.
Platform Context
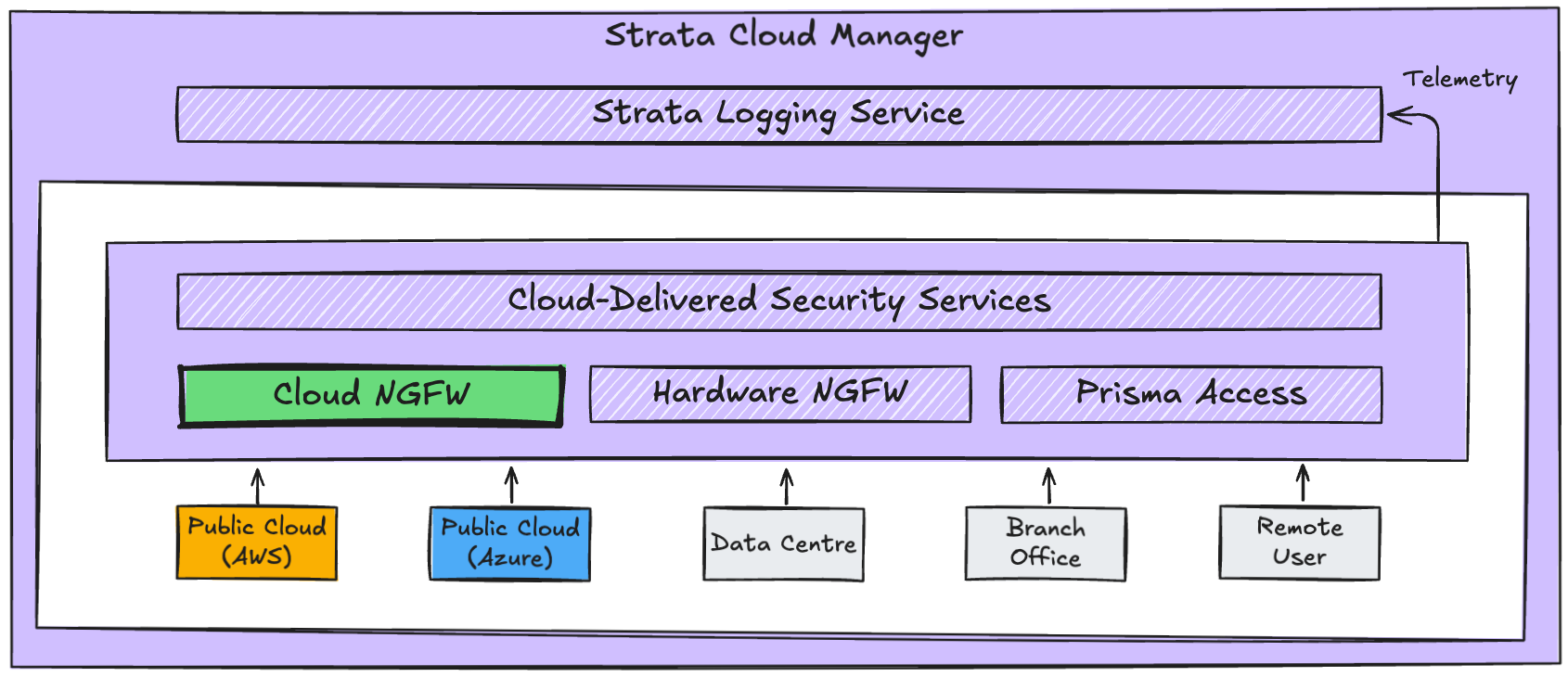
Within the Palo Alto Networks NetSec platform, Cloud NGFW is a cloud-native enforcement layer, extending platform capabilities into AWS and Azure public clouds.
It serves a different purpose to hardware NGFW and Prisma Access, but shares common platform capabilities. Management and policy remains centralised through Strata Cloud Manager (SCM). Telemetry is normalised into the same data model. Inspection capabilities are delivered consistently through Cloud-Delivered Security Services (CDSS).
Operational Overview
Cloud NGFW is a cloud-native firewall service fully managed by Palo Alto Networks and deeply integrated into the fabric of the cloud providers infrastructure, enabling:
- Layer 7 application visibility and control
- Identity-aware policy enforcement
- Decryption and content inspection
- Malware and threat prevention
- Segmentation across and within VPCs or VNets
- Consistent policy across hybrid and multi-cloud environments
At its core, the service extends familiar NGFW capabilities into cloud environments. Importantly, it does so within the context of cloud-native constructs and APIs.
This includes:
- Route table manipulation and traffic steering
- Integration with identity providers
- Use of cloud metadata (tags, labels, instance attributes)
- API-driven policy updates and automation
Since the Cloud NGFW is delivered as a service, the operational overhead of infrastructure and lifecycle management is removed. Traditional sizing exercises and manual high-availability deployments are no longer needed.
Operationally, Cloud NGFW:
- Scales for throughput automatically
- Handles upgrades and planned maintenance automatically
- Handles outages and unplanned maintenance automatically
- Handles availability zone resilience and affinity automatically
Due to the first-party nature of the service, cloud teams are able to include the resource in their existing cloud-native processes and controls for automation, deployment, billing, logging, and security.
Architecture Overview
The Cloud NGFW service introduces some new terminology:
Cloud NGFW tenant: a logical management container per customer and per cloud-provider. The tenant can be linked to Strata Cloud Manager (SCM) for centralised management, policy, and visibility.
Cloud NGFW resource: the data plane that carries out traffic inspection and firewall capabilities. The resource is a regional service with built-in resilience and is dedicated per tenant to ensure traffic processing is kept separate from other customers.
Behind the scenes, the Cloud NGFW resource runs in a Palo Alto managed environment. Depending on the AWS or Azure variant there are some nuances in the way the back end service is built and traffic is steered.
At a very high level, the AWS deployment is a VPC endpoint service and Azure uses User Defined Routes (UDR) and/or Intent Based Routing (IBR). This difference is down to how each cloud-provider controls traffic steering. AWS leans on service endpoints, whereas Azure relies more explicitly on route control within the customer environment.
In both cases, the routes are defined by the customer, and the cloud-provider private backbone network is used between the customer environment and the Palo Alto managed environment.
There are 2 main deployment topologies for the Cloud NGFW:
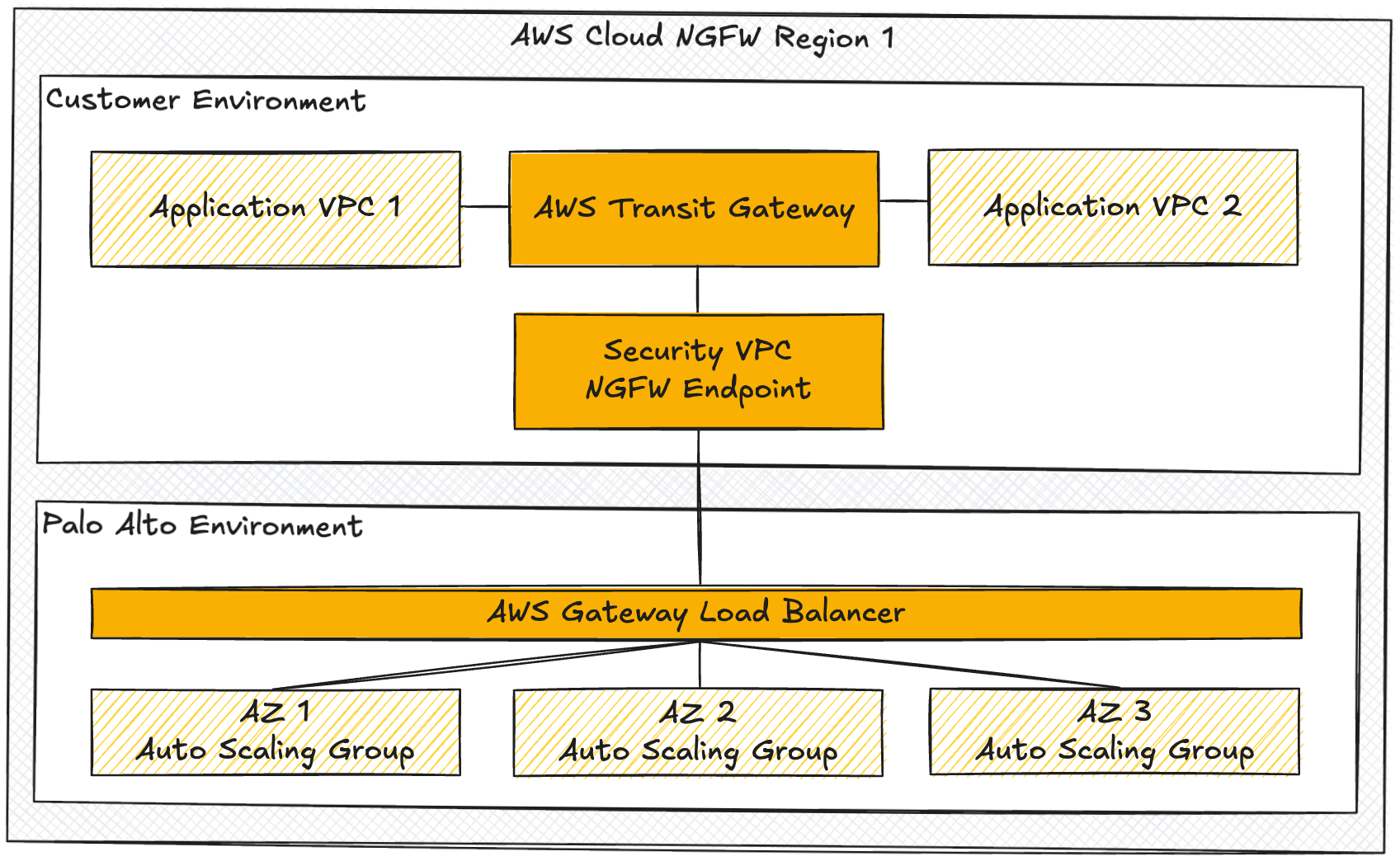
- Centralised Topology
Where a hub and spoke network design is in place, a centralised security VPC or VNet makes the connection to the Cloud NGFW resource. This approach simplifies connectivity and scales well.
The example below shows the high level components for a centralised topology in AWS. Azure uses a similar model with either a VWAN hub or VNet hub design.
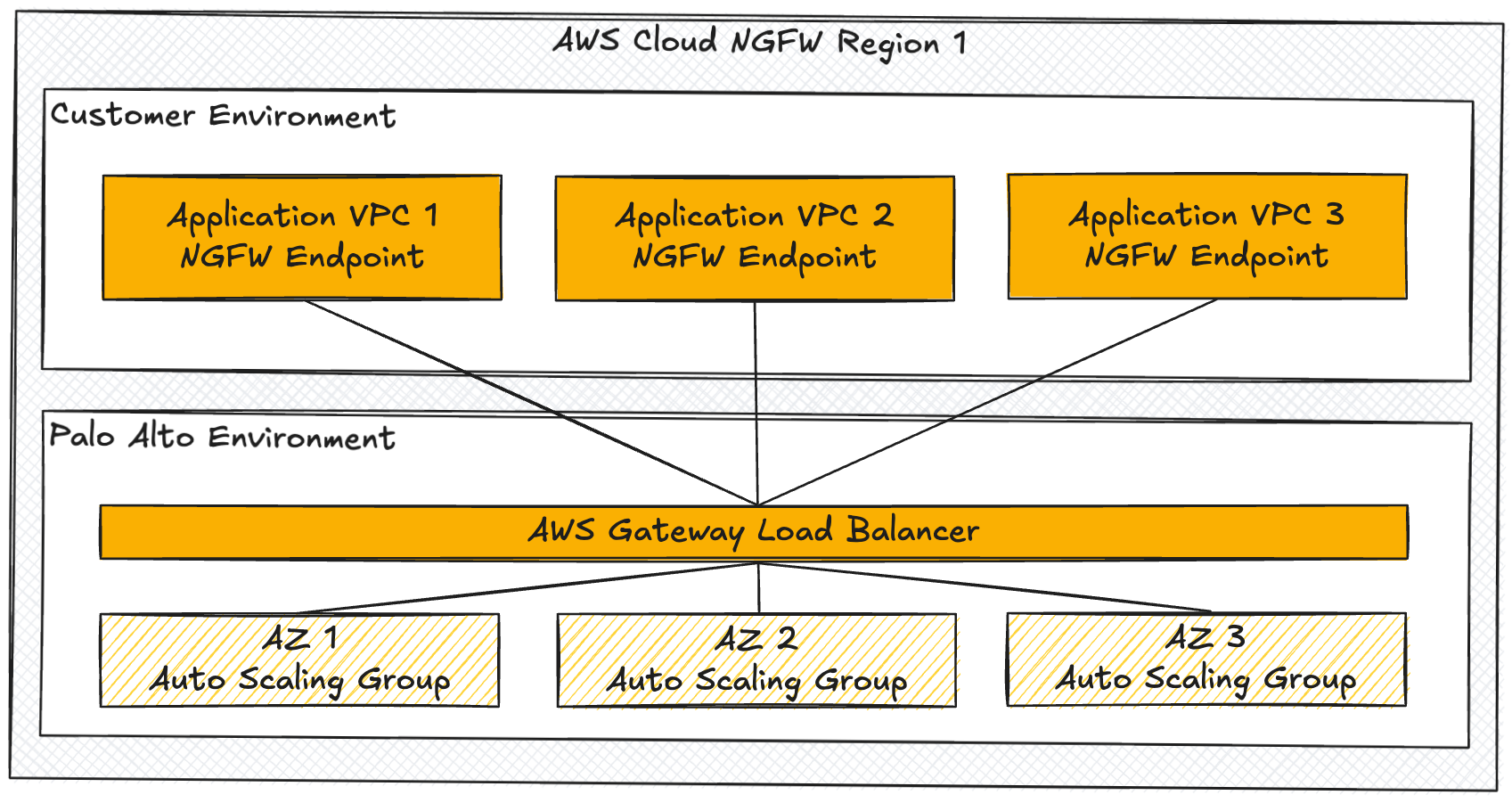
- Distributed Topology
In a distributed topology each VPC or VNet requiring inspection creates a direct connection to the Cloud NGFW resource. This approach doesn't scale as well as the centralised topology, since it requires ongoing manual configuration. However, it is useful for certain use cases and isolated or smaller environments.
The example below shows the high level components for a distributed topology in AWS. Azure uses a similar model with each VNet connecting directly to the Cloud NGFW resource.
More detailed reference architectures can be found in the Palo Alto Live Community pages below.
Operational Scenario
Scenario: An attacker exploits a vulnerable application on an EC2 instance that has outbound internet access. Malware is used to initiate a Command-and-Control (C2) beacon within normal encrypted outbound application traffic.
With standard cloud-provider controls:
- Security groups and NACLs only have network-level visibility and allow the outbound HTTPS connection
- Traffic is not decrypted for full payload inspection by native controls, so remains encrypted and outside effective inspection
- Attacker now has an active presence with C2
- Attacker moves on to credential theft, privilege escalation, lateral movement, and data exfiltration or destruction
With Cloud NGFW:
- TLS decryption is performed and traffic inspected inline by the Cloud NGFW
- Malicious traffic or C2 behaviour is detected through a combination of decryption, threat intelligence, and behavioural analysis
- Session is blocked in real time and the potential breach is contained at an early stage
- Alert and optional automated response is triggered
Some of the built-in cloud tools can detect and even partially restrict malicious activity. The Cloud NGFW closes the gap with context and application-aware inline enforcement.
Platform Outcomes
Cloud NGFW represents a shift from network-centric security to application and context-driven enforcement within cloud environments.
In practice, this results in:
- Consistent policy across environments
- Improved visibility into application and workload behaviour
- Greater overall threat protection
- Reduced operational overhead
- More granular access control
- Stronger alignment with Zero Trust principles
